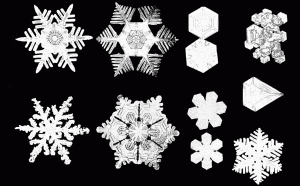
Every snowflake is different!
goes the saying. This can be used to fight counterfeiting of physical objects.
Continue reading
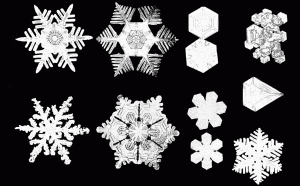
Every snowflake is different!
goes the saying. This can be used to fight counterfeiting of physical objects.
Continue reading
I recently had a problem with my website zimmer69.de. Some not so nice fellow told his opera browser to reload a 300k page every 5 seconds, moved it to some tab and forgot about it for weeks. He caused 2 Gb of traffic per day. Time to implement some cache control.
Continue reading
This post describes how to encrypt the home directory of your users on GNU Linux with the help of TrueCrypt and PAM using the login-password as encryption key.
I wrote about Automatic encryption of home directories using TrueCrypt before. This time we’ll use TrueCrypt 6.2a. Futhermore we’ll use Ubuntu 9.04 Jaunty Jackalope and we replaced pam_mount by pam_exec. For convenience this post will be selfcontained (ie. I copy redundant parts from the old one).
Continue reading
The String#constantize method is a feature that makes rails fun to code with. This method converts a string to the constant that the string contains (or throws a NameError if there is no such constant). It makes it easy to store class-types in databases as strings and to code controllers that work with classes of the same duck type.
Most people know that eval on user data is dangerous, but noboddy seems to care about constantize. Beware, it is also dangerous and you should constantize with care!
Continue reading
I recently found a shell injection bug in some Ruby-gem I use.
Shell injections have scared me for a long time and I usually prefer to whitelist certain characters/patterns rather than to blacklist. This means that the system fails to the save side. Unfortunally it usually does fail – my whitelisting is to rigorous and data that would not cause any problems gets rejected. So I decided to take the opportunity to investigate how to prevent shell injection in my favorite scripting language (Python), the language I found the problem in and finally the language that I can not avoid (PHP).
Having your private data on a laptop is dangerous, since it might be stolen. The only way to protect your data is to encrypt it. This post describes how to encrypt the home directory of your users on GNU Linux with the help of TrueCrypt and PAM. For convenience the login-password is used as encryption key. Continue reading